-
27 Apr 2022
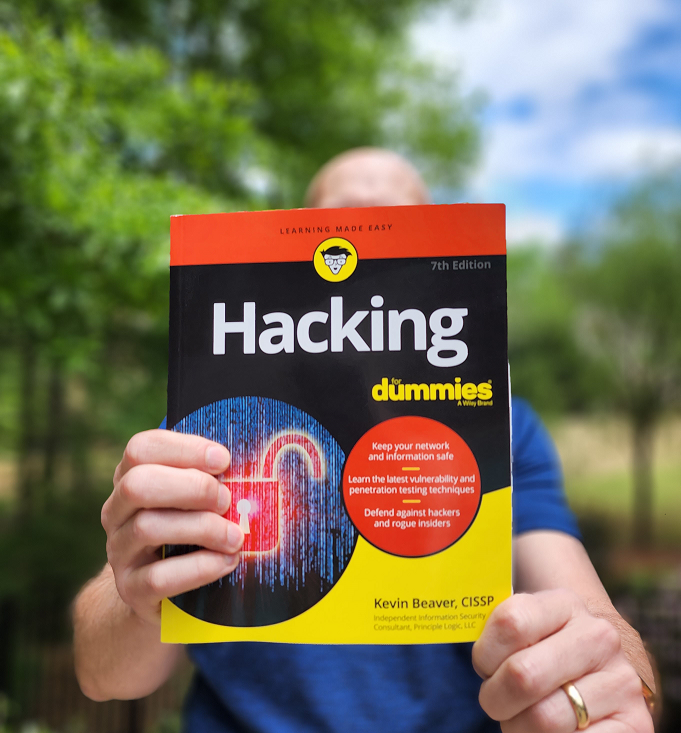
It’s here! Hacking For Dummies, 7th edition
Hot off the press, the latest (7th) edition of my best-selling book on security vulnerability and penetration testing, Hacking For Dummies, is here! Hacking For Dummies is one of the oldest and most successful books on information and computer security and, as of 2019, it has been translated into 9 different languages. Who would've thought all the blood, sweat, and tears that I put in to the first edition of ...
Continue Reading... -
11 Apr 2019
WP Security Audit Log – a must for WordPress security oversight and resilience
Not long ago I moved my information security consulting business website to WordPress - something I thought I'd never do. The burden of hosting it myself combined with the hassles of working with Dreamweaver forced the change. I wasn't initially a big fan of WordPress...it's almost too much to take on. This coming from a technical guy who hosted Apache on Windows and did most of my administration at the ...
Continue Reading... -
21 Dec 2017
Web application and mobile app security testing – Are you on board?
Here are some recent pieces I've written regarding web application and mobile app security based on the work I do that you might be interested in: How security controls affect web security assessment resultsThe importance of integrating mobile apps into your security programHow automated web vulnerability scanners introduce risksAddressing web server security vulnerabilities below the application layerDon’t sweep web application testing under the rugYou may not be in control but ...
Continue Reading... -
26 May 2017
From web to mobile to connected cars – here are some application security resources you need to check out
Given all of the variables and complexities associated with information security, I still believe that application security is the biggest weakness in most organizations and the one area where we can truly effect the greatest change. Here are some pieces that I have written recently regarding web and mobile app security that you might enjoy:Identifying and addressing overlooked web security vulnerabilitiesWhat the end of hot patching mobile apps means for ...
Continue Reading... -
13 Apr 2017
Why SOC audit reports can be misleading, mobile app security gotchas, and more…
Here are some links to recent articles I've written regarding application security...if you take anything away from this, it's that you can't afford to take this part of your security program lightly. Dealing with vendors who want to push their SOC audit reports on you Explaining discrepancies in different security assessment reports Why DAST and SAST are necessary if software is solid from the get-go Nixing credential re-use across unrelated ...
Continue Reading... -
13 Mar 2017
Web and mobile application security vulnerability and penetration testing resources
Application security is no doubt one of the most important aspects of a security program. Here are some new pieces I've written that can help keep your web and mobile app vulnerabilities in check and your application security program on the right track...pay special attention to the last one regarding security assessments and reality:Keeping your Web applications in check with HIPAA complianceMobile app security risks could cost you millionsCommon oversights ...
Continue Reading... -
24 Aug 2016
A WordPress security resource for you: WP Security Audit Log
WordPress has had its fair share of security flaws over the years. Arguably more than any other mainstream platform. A quick search of 'wordpress' at the National Vulnerability Database returns over 1,100 published vulnerabilities as old as 2004 and several as recent as this month. Despite all of the security issues, WordPress is a highly-popular platform for businesses and individuals alike to create their online presence.There are a lot of ...
Continue Reading... -
25 Apr 2016
New content on web application security testing
Here are a two brand new pieces I've written on web application security recently for the nice folks at TechBeacon:Why ALL of your apps need security testing4 insider tips for choosing application security testing toolsMore to come - you can link/subscribe to my author page here. Enjoy!...
Continue Reading... -
20 Apr 2016
What you need to know about Checkmarx CxSAST version 8
Application security tool version upgrade usually don't excite me as it's often the same old, same old with a few new checks and niche features. However, the new version of Checkmarx CxSAST (formerly CxSuite, CxDeveloper, etc.) is spot-on. The next generation of the popular static source code analyzer - version 8 - was recently released and it contains some much-needed improvements over its predecessor. One thing that's glaringly evident in version 8 ...
Continue Reading... -
10 Mar 2015
Using Checkmarx CxSuite to outline “the rest of the story” regarding application security
When it comes to Web application and mobile app security, can you honestly say you know where everything stands...as American radio personality Paul Harvey used to proclaim - the rest of the story? You can run Web vulnerability scans, perform manual mobile app analysis, and the most in-depth penetration testing possible. You can look at things from the perspectives of unauthenticated attackers, trusted users, and all the angles in between ...
Continue Reading...