-
15 Oct 2025
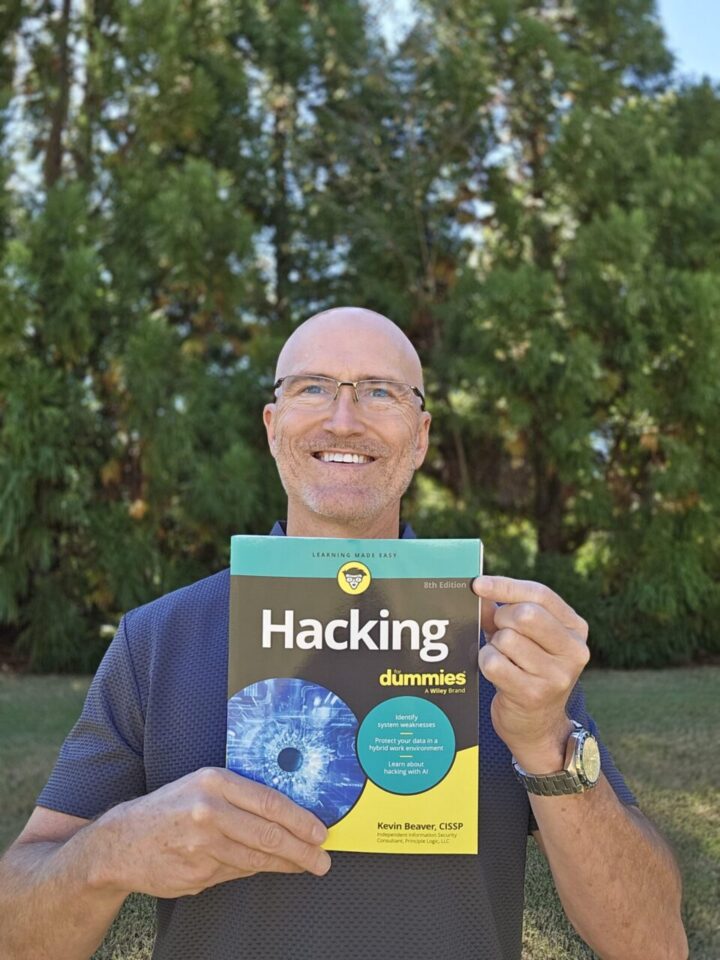
Hacking For Dummies, 8th edition…It’s official!
After months of writing, revising, and updating real-world examples, Hacking For Dummies, 8th Edition is finally out in the wild.👉 Get it here on Amazon (affiliate link) This book has been a part of my professional life for over two decades now. Thanks to you — my readers, clients, and colleagues — it’s been translated into nine languages and remains the top-selling book in its category over the past decade. ...
Continue Reading... -
16 Feb 2022
Macs are secure…no need to test them?? You might want to rethink that approach.
Macs are secure! Right...? They don't really need to be tested...including them in an overall vulnerability management program is likely overkill. It's an age-old philosophy coming from those who need some enlightenment...perhaps get caught up on their reading. The next time someone tells you that macOS is secure, respectfully push back and ask: How do you know? Here's a screenshot of the Tenable.io findings from just one scan of a ...
Continue Reading... -
19 Mar 2019
Good, old-fashioned, boring passwords – the key to good security
Many people are quick to proclaim that passwords are dead...that SSO, MFA, and related technologies are THE solution. Not so fast. Passwords, as we've known them for decades, are not going away anytime soon. Sure, I'll embrace the technologies that help take the pain out of passwords and password management. Hopefully we will be password-free in the next few decades. Still, pragmatism will win out over presumed quick fixes every ...
Continue Reading... -
07 Feb 2019
Hacking For Dummies now in its 9th language
I just found out from my publisher, Wiley, that my book Hacking For Dummies is being published in Dutch. That makes the ninth language for my book since its inception way back in 2003. Here's the full list of languages: English German (including the new 6th edition)DutchHindiFrenchPortugueseSimplified ChineseItalianBulgarian I'm eager to see what the next language will be! I really hope you'll check out my book. Of course, I'm a ...
Continue Reading... -
07 Aug 2017
How to gain control & become an IoT security expert
You've no doubt heard the vendor spiels and seen their solutions for gaining control of your Internet of Things environment. But do you truly have IoT under control? Like other things in IT, it can be pretty overwhelming, especially when you're struggling to keep your arms around your traditional network environment with cloud and mobile and all the complexities they bring. Well, IoT security doesn't have to be that difficult. It's ...
Continue Reading... -
13 Apr 2017
Why SOC audit reports can be misleading, mobile app security gotchas, and more…
Here are some links to recent articles I've written regarding application security...if you take anything away from this, it's that you can't afford to take this part of your security program lightly. Dealing with vendors who want to push their SOC audit reports on you Explaining discrepancies in different security assessment reports Why DAST and SAST are necessary if software is solid from the get-go Nixing credential re-use across unrelated ...
Continue Reading... -
03 Mar 2017
Email phishing services: Just what you need to know to start mastering the task
Got phished? Of course you have...whether you know it or not! As with penetration and vulnerability testing and any other form of security assessment, you need to be performing email phishing tests on your users – all of them, including executive management – on a periodic and consistent basis. I'm doing more and more of this work and the results that I'm finding are astounding...to the point that all other security ...
Continue Reading... -
05 Dec 2016
Using NowSecure for automated mobile app testing
As an independent information security consultant, I'm always looking for good testing tools to rely on for my work. These tools, such as vulnerability scanners, network analyzers/proxies, and related manual analysis tools, are not the be-all-end-all answer for uncovering security weaknesses, but they are a very important aspect of what I do. Be it more generic vulnerability scans, a targeted penetration test, or a broader, more in-depth, security assessment, I ...
Continue Reading... -
24 Aug 2016
A WordPress security resource for you: WP Security Audit Log
WordPress has had its fair share of security flaws over the years. Arguably more than any other mainstream platform. A quick search of 'wordpress' at the National Vulnerability Database returns over 1,100 published vulnerabilities as old as 2004 and several as recent as this month. Despite all of the security issues, WordPress is a highly-popular platform for businesses and individuals alike to create their online presence.There are a lot of ...
Continue Reading... -
12 Aug 2016
Penetration Testing and Security Assessment Essentials…Don’t ignore this stuff.
Want tips on how to perform better security assessments and penetration tests? Here you go:What are the most important security testing basics?Determining your scope of security testingBest Practices and Tips for Choosing Application Security Testing ToolsWhy ALL of your Web applications need security testingIt can be dangerous assuming a vulnerability is not a vulnerabilityWhat constitutes a “critical” security flaw?Rely on data center audits alone and you’ll get hit eventually What ...
Continue Reading...