-
The Epstein Files and the email footer that changed nothing
04 Mar 2026“Here is a rich man who is the victim of a painful and persistent disease as the result of gluttony. He is willing to give large sums of money to get rid of it, but he will not sacrifice his gluttonous desires. He wants to gratify his taste for rich and unnatural viands and have his health as well. Such a man is totally unfit to have health, because he has not yet learned the first principles of a healthy life.” — James Allen, As a Man Thinketh
An email footer is not a privacy or security control. But you wouldn’t know that from the way people treat them.
The word CONFIDENTIAL appears at the bottom of emails across virtually every industry. Bolded. Legal-sounding. Sometimes threatening. Management feels covered. Legal feels protected. Checkbox checked.
What actually happens? Emails stamped “CONFIDENTIAL” get forwarded casually, downloaded onto unmanaged devices, and stored indefinitely with zero oversight. No classification standards behind the label. No technical controls restricting access. No auditing to verify how information is handled. The footer creates the appearance of protection while giving people plausible deniability as the proper governance work is left undone.
That disconnect became especially clear when emails surfaced in the Epstein document disclosures, including correspondence from Peter Attia, M.D., complete with a formal confidentiality footer warning that the information was privileged, protected by federal and state privacy laws, and not to be disseminated. Strong language. Authoritative tone. Not meant for public consumption.
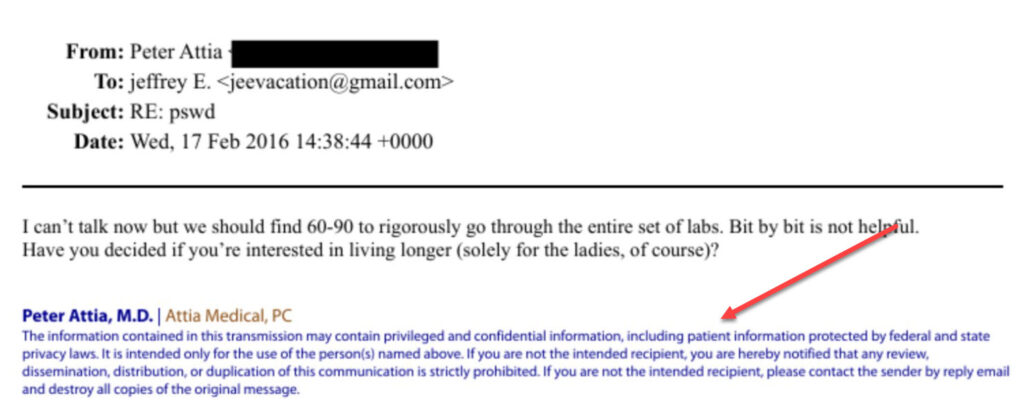
Yet there it is, publicly available for anyone to read…
None of that changes how email technology works. A confidentiality disclaimer doesn’t override messaging systems, backups, screenshots, subpoenas, or leaks. It doesn’t prevent forwarding or stop recipients from mishandling content the moment it hits their inbox. And it does nothing to address sender-side risk. If the sending system lacks proper security controls, full-disk encryption, enforced access policies, the email is exposed before it ever reaches the recipient. Legal language at the bottom of a message is not a substitute for any of that.
This brings James Allen’s quote into focus. The assumption that wealth, status, or professional prominence changes how technology works is its own form of indulgence. I wrote about Mark Zuckerberg after his Twitter and Pinterest accounts were compromised because he reused a weak password across multiple platforms. Even tech-savvy people make elementary security mistakes while projecting control. The Epstein disclosures are just the most recent example.
The irony runs deeper. Executives and high-profile individuals are routinely exempt from the security policies that govern everyone around them. Yet they are the highest value targets. The more prominent someone is, the more attractive their data becomes, but the reliance on legacy email habits, unmanaged devices, and sloppy governance continues.
Something else related to this: sending a “secure” link via email to download a document while requiring no credential verification beyond clicking the link. Even platforms that require authentication aren’t as secure as people assume unless multi-factor authentication is enforced. A password alone isn’t sufficient. Without MFA, a “secure” system is often only marginally more protected than one with no access controls at all. If you’re concerned about email exposure, enforce authentication and access controls that reflect those risks. Otherwise you’ve added busywork without meaningful protection.
Modern email infrastructure from major providers is secure in transit. TLS encryption is widely enforced. The problem isn’t data in transit. It’s the before and after. Once an email lands in an inbox, synchronizes to multiple devices, gets backed up, exported, or screenshotted, control becomes impossible. If those devices aren’t using full-disk encryption, one of the most effective baseline controls available is simply not in place.
Information classification and governance have been around for decades. If you intend to protect confidential information, think it through rather than slapping a label on something and hoping for the best. I’ve worked enough breach projects and legal cases as an expert witness to know that investigators and opposing counsel don’t care what your email footer said. They want to know what you actually did.
If confidentiality and privacy are genuine priorities, build the habits and systems that reflect those principles. If they aren’t, don’t pretend that a paragraph at the bottom of an email makes it so.
Perhaps the biggest takeaway: do good in this world and you won’t have to worry about these kinds of things.



