-
21 Jun 2017
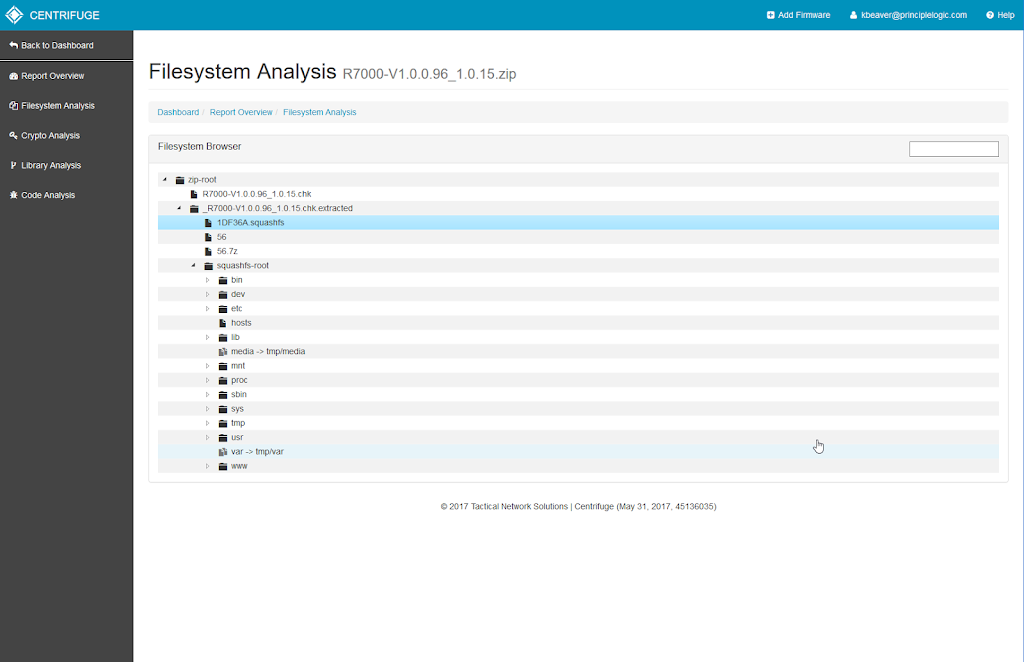
Using Centrifuge for IoT security testing
I love hacking things, especially new things like what's showing up on networks around the globe in the form of IoT. If IoT security is anywhere on your radar, you're likely incorporating these devices into your security testing program. Well, there's a new IoT security assessment tool in town that you need to know about called Centrifuge brought to you by Tactical Network Solutions - makers of the former (and ...
Continue Reading... -
26 May 2017
From web to mobile to connected cars – here are some application security resources you need to check out
Given all of the variables and complexities associated with information security, I still believe that application security is the biggest weakness in most organizations and the one area where we can truly effect the greatest change. Here are some pieces that I have written recently regarding web and mobile app security that you might enjoy:Identifying and addressing overlooked web security vulnerabilitiesWhat the end of hot patching mobile apps means for ...
Continue Reading... -
09 Aug 2010
How you can get developers on board with security starting today
Some people - including a brilliant colleague of mine - think security is not the job of software developers. In the grand scheme of things I think such an approach is shortsighted and bad for business. It's kind of like an auto assembly line worker not being responsible for the quality of his work or citizens not being responsible for their own healthcare (oh wait!) or why the bottom 50% ...
Continue Reading... -
02 Apr 2010
THE process for successful Web security testing
Here's a new piece I wrote for SearchSoftwareQuality.com where I talk about the lifecycle of testing for Web security flaws. From obtaining buy-in to reporting to the stakeholders, it's a process you need to master.Security testing best practices for today's Web 2.0 applications...
Continue Reading... -
29 Jun 2009
Great source code analysis tool
Finally, I've found an affordable and effective static source code analysis tool! It's called CxDeveloper - a product Israel-based Checkmarx that's distributed/supported by U.S.-based Security Innovation. Whew....it's a little confusing but what can you do.I've used CxDeveloper for over a year now and, like most products, it's not perfect. It crashes unexpectedly every now and then, it generates false-positives, its licensing process is kludgy and old-fashioned, and its reporting capabilities ...
Continue Reading... -
23 May 2008
My security content from this week
Here's my one information security article that was published this week:Writing software requirements that address security issuesAs always, for my past information security content be sure to check out www.principlelogic.com/resources.html.Enjoy!...
Continue Reading...