-

The key to accurate and insightful Web security scans
07 Sep 2010You’ve likely found that Web vulnerability scanners aren’t just point-and-click. Maybe so for relatively simplistic marketing websites but not for complex applications. In fact, one of the greatest ways to get a grand false sense of security is to turn a Web vulnerability scanner loose on your site/application and assume everything of consequence has been discovered and audited.
The thing is we’re now seeing an entirely new set of Web applications that just aren’t that simple to assess with an automated tool. Be it an online survey, e-signing application, or e-commerce system if the scanner doesn’t know where to go (or client-side Web 2.0 code trips it up) you’re going to get a whole lot of nothing in the results column.
Making the problem worse is the fact every application is different…often vastly different. Not just the platform and the coding but the logic and the workflow. It’s all those manual clicks in/around the app combined with tons of Ajax, Flash, and other code that’s almost impossible for a scanner to traverse that really complicates things. And it’s a problem that’s not going away.
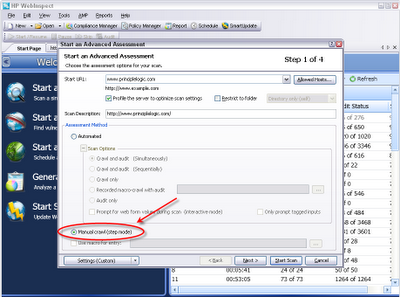
There’s one Web vulnerability scanner that has always helped to take the pain out of this process – at least as long as I can remember. That scanner is HP’s WebInspect. Performing a manual scan using WebInspect is very simple: you load up a new scan, tell it you want to perform a “Manual Crawl” as shown in the following screenshot and you’re good to go.
Once you kick the scan off, WebInspect automatically loads Internet Explorer for you to step through the application. Meanwhile, in the background, the scanner captures every page you browse to, every input you provide (login credentials included), and every script that’s run. Once you’re done you simply close out Internet Explorer and WebInspect should complete its crawl (you may have to click Finish). If the application logs the scanner out, WebInspect will automatically log itself back in.
[Side note: This assumes that Default Audit Mode under Edit/Application Settings/Step Mode is set to Manual Audit (which I prefer). Otherwise the audit will have already started during the crawl phase and may complete (you sometimes have to pause the scan and restart for it to complete)].
Once that’s done, you’ll then click the red Audit button, select the audit policy you want to use, and WebInspect will continue on testing the pages it crawled for vulnerabilities. That’s it.
It’s still up to you to know and understand the logic and workflow of the application you’re assessing. If you don’t step through the application in the right ways or overlook critical parts of it, you can’t blame the scanner for not providing good results. It will if it knows where to look and what to look for.
Bottom line: you absolutely cannot rely on the results of a basic Web “scan” in the name of PCI DSS compliance or whatever. You have to use a good scanner…in all the right ways. No one ever said it was easy. But done right, the payoffs are worthwhile.



