-

LUCY – a very powerful email phishing tool
25 Jan 2016If you’re an IT or information security professional you need to know about a great – and relatively new – tool that you can use as part of your security assessment and/or user awareness and training programs…it’s called LUCY. I came across a small online blurb about LUCY a few months ago and thought I would check it out. Having dealt with both open source and commercial email phishing tools that have either gone kaput or the vendors have no interest in serving an independent consultant like myself, it looked like LUCY might be just what I needed. It is.
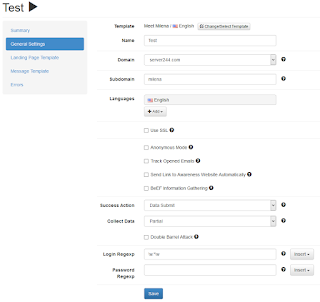
Available as a virtual machine download or an application running in the cloud, LUCY supports traditional email phishing campaigns but it goes several steps further by supporting SMiShing (SMS phishing), the simulation of malware attacks, Word macros, and it has a bunch of other features. LUCY’s reporting capabilities are nice as well. The following is a sample of one page of the LUCY Web interface and you can see more for yourself here.
Before I discovered LUCY, I was seriously considering hiring a developer to write my own email phishing tool. I’m glad I didn’t because I would have missed a whole lot of features that I never would‘ve thought about. I’m also confident that I would’ve ended up getting in over my head with such a project. That’s the great thing about working in this industry – I get to rely on the brainpower, findings, and products of all of the researchers and developers who are way smarter than me.
LUCY’s feature set is nice but, to me, the best part is the support that I have received from its Swiss-based creator, Oliver Münchow. Oliver was very responsive and extremely patient with me as I got my environment up and running. In fact, I bugged him with so many DNS/SMTP configuration and user workflow questions (when, in many cases, I should’ve read the fine manual) he told me that he obviously needs to make some tweaks to the documentation and the functionality of the program. 🙂 He already has. Pretty cool.
Studies from Verizon, Trustwave, and others all show that social engineering via email phishing is one of the most popular attacks. It‘s just too simple and too effective. Many (most?) businesses today are making it too easy for criminal hackers to carry out their malicious acts for ill-gotten gains. I’ve been doing this type of work more and more as part of my overall security assessment projects and the results are pretty scary. If you’re not doing email phishing testing, you can’t honestly say that you’re looking at everything – testing for all possible vulnerabilities – in your environment.
Whether you work for someone else or for yourself, you should check out LUCY if you‘re in need of simple to use, yet powerful, email phishing and security awareness/training campaign capabilities that you can get up and running almost immediately. Minimal technical expertise is required. Maximum value is pretty much guaranteed.
You can check out more about social engineering and email phishing (tips, tools, and techniques) in the brand-new 5th edition of my book, Hacking For Dummies.