-
30 Apr 2021
Networked IP cameras as vulnerable as ever…no excuses these days.
You've likely heard the news about security cameras being vulnerable to exploits like what was covered in this piece: https://threatpost.com/breach-verkada-security-camera-tesla-cloudflare/164635/ I feel like I'm always talking in circles when it comes to security...stop repeating history, focus on the basics, do what you know needs to be done...It's especially true for vulnerabilities in network security cameras. A little over nine years ago I wrote about this problem with cameras that I ...
Continue Reading... -
30 Apr 2019
Healthcare’s latest (ridiculous) proposal to improve security in that industry
For years, I've ranted about the rebranding of information security to "cybersecurity". This strategy is nothing more than a means to redirect attention - even create confusion - over what we do so that something shiny, new, and sexy can be sold to those who are buying. It's bad for what we're trying to accomplish in this field. We need less confusion rather than more. Well, here's a new set ...
Continue Reading... -
12 Sep 2018
Using Securolytics for enhanced IoT security
I often say that you can't secure the things that you don't acknowledge...I can't imagine that reality applying to anything in IT or security as much as it applies to securing Internet of Things (IoT) devices that are on your network, creating risks...this very moment. The trouble with IoT devices that they can be not only hard to discover and manage but they're also extremely difficult to identify. Oftentimes, in ...
Continue Reading... -
07 Aug 2017
How to gain control & become an IoT security expert
You've no doubt heard the vendor spiels and seen their solutions for gaining control of your Internet of Things environment. But do you truly have IoT under control? Like other things in IT, it can be pretty overwhelming, especially when you're struggling to keep your arms around your traditional network environment with cloud and mobile and all the complexities they bring. Well, IoT security doesn't have to be that difficult. It's ...
Continue Reading... -
21 Jun 2017
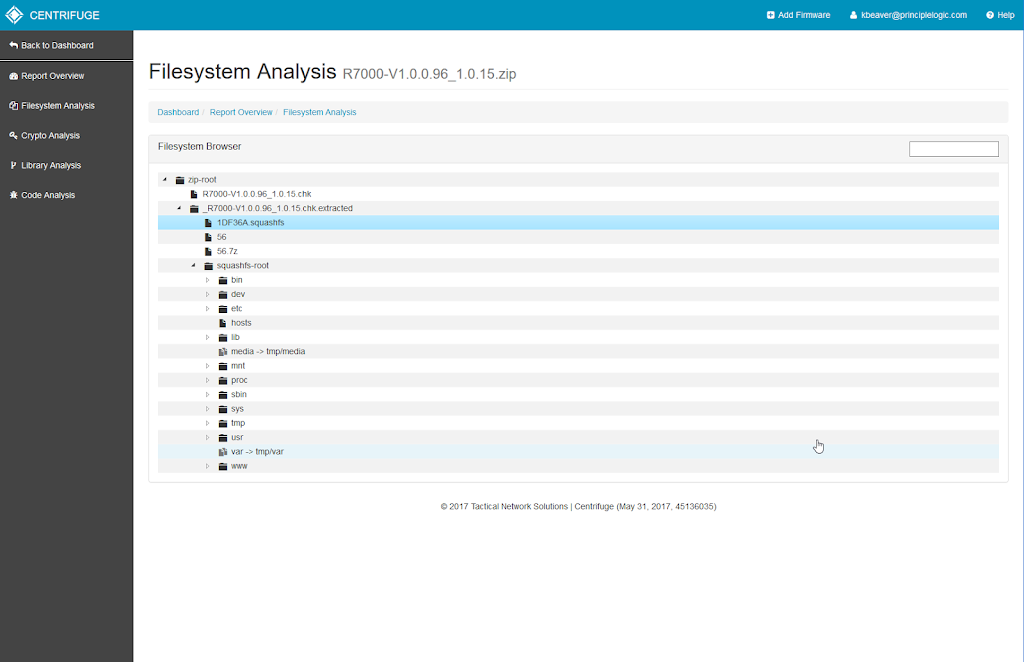
Using Centrifuge for IoT security testing
I love hacking things, especially new things like what's showing up on networks around the globe in the form of IoT. If IoT security is anywhere on your radar, you're likely incorporating these devices into your security testing program. Well, there's a new IoT security assessment tool in town that you need to know about called Centrifuge brought to you by Tactical Network Solutions - makers of the former (and ...
Continue Reading... -
26 May 2017
From web to mobile to connected cars – here are some application security resources you need to check out
Given all of the variables and complexities associated with information security, I still believe that application security is the biggest weakness in most organizations and the one area where we can truly effect the greatest change. Here are some pieces that I have written recently regarding web and mobile app security that you might enjoy:Identifying and addressing overlooked web security vulnerabilitiesWhat the end of hot patching mobile apps means for ...
Continue Reading...